The adoption of OPC UA technology continues to grow more with each passing year. And for good reason. OPC UA provides a means to encrypt data as it is transferred between client and server that other client interface options simply do not. But when it comes time to have that discussion with your IT department around whether they are going to let you run OPC UA inside the firewall on a network, they likely will have concerns centered around common IT concerns in networks.
Continuing our Tech Support Corner blog series, this post covers some common concerns that our support engineers have encountered from process engineers collaborating with their IT department about OPC UA client's and servers running on their network and the factors to consider in those discussions.

The Port Danger
Let's start by asking the obvious question. Are your IT Network admin’s concerns about opening a port valid? Yes! Absolutely. Attacks on manufacturing systems, utilities, critical infrastructure, and supply chains continue to grow, and it is my firm belief that there is no such thing as an impenetrable network or system. You must secure the network and stay a step ahead of a potential attacker and consider novel approaches to how to move data securely.
Although not perfect, and there are other ways we will cover in our next blog post that are even more secure, OPC UA does only require a single open port which compared to DCOM is less risky but not without risk.
It is also important to consider are you opening a port to the outside world or within your outer perimeter firewall or between network segments? Opening any ports is a risk for sure, but opening ports to the outside world is a bad idea that I don't recommend unless that's your only choice. If you do that then you must limit the scope to known IP addresses and employ a whole host of other measures that are outside the scope of this blog post.
 Don't want to open any ports? We will also be discussing how to integrate OPC UA without opening ports, using DataHub, in an upcoming blog post. If you want to start now, you can start learning how DataHub Tunneling can help.
Don't want to open any ports? We will also be discussing how to integrate OPC UA without opening ports, using DataHub, in an upcoming blog post. If you want to start now, you can start learning how DataHub Tunneling can help.
Does OPC UA Communications cause broadcast traffic?
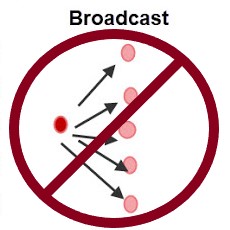 Broadcast traffic on a network is bad, so when IT asks you this question, they are asking for a good reason. Broadcast traffic can take a network to it's knees, which can take a business or plant offline.
Broadcast traffic on a network is bad, so when IT asks you this question, they are asking for a good reason. Broadcast traffic can take a network to it's knees, which can take a business or plant offline.
OPC UA uses a TCP port, which is socket-based, as opposed to UDP. UDP, which is connectionless is typically used for broadcast messages where a connection to the receiving host/hosts is not required first (for example, the SNMP protocol commonly uses UDP).
By nature of OPC UA using TCP for communications, the threat of broadcast traffic is eliminated.
Now there is obviously a lot more to OPC UA than our basic answers to these common IT concerns. For a more detailed look at OPC UA security handling, I would encourage you to have a look at our Exploring OPC UA blog series and download the free whitepaper on OPC UA security concepts. It provides a good overview of how OPC UA certificates are utilized, how encryption works and the security layers of the OPC UA protocol (of particular relevance here).
And don't forget to subscribe to our blog to find out about more relevant technical topics applying to industrial process automation and to receive our next post on "How to move OPC Data without opening inbound Open Firewall Ports to your Production Network".
