Over the last several years, it has become a beloved tradition to start the new blog year with a review of the most popular content the team at Software Toolbox put together to build your automation software skills and empower your success. This is the 8th installment of this blog summary covering a wide variety of topics. But first things first: make sure you are subscribed to our blog. We publish new content at least once a week, and you have full control over the frequency of when you are notified.
Software Toolbox Technical Blog
2025 Automation & Control Software Learning Resources
10 min read
By Tanja Gehling on Jan 16, 2025 2:00:00 PM
2024 Automation & Control Software Learning Resources
8 min read
By John Weber on Jan 25, 2024 2:00:00 PM
Welcome to our most popular blog post of the year! Each year we publish this blog post to help you learn, grow, and support empowering you to improve your business.
This post is our 7th annual sharing of references to learning resources including our ever hot Tech Support Corner, popular technical blog posts, and product capabilities that users have told us were the most helpful to them over the course of the last year.
2023 continued the challenges in supply chain, inflation, labor shortages, and exploding customer demand and in many cases technology continues to be a key part of dealing with the challenges.
Tech Support Corner: Understanding DNP3 Polling Behavior Basics
7 min read
By Kevin Rutherford on Mar 16, 2023 2:00:00 PM
The DNP3 protocol is commonly used in water/wastewater and other utilities related industries. It's common for RTUs used in these industries to support both DNP3 and Modbus (and possibly other communications protocols). DNP3 has many features compared to Modbus (and other more traditional protocols) that make it desirable for such remote telemetry applications including buffered event history and unsolicited (or Report-By-Exception).
But if you're new to working with DNP3 (it's common for users in such industries to be quite familiar with Modbus but not so familiar with the quirks of DNP3), it's important to understand how differently it behaves with respect to polling frequency, polling composition and considerations when configuring the DNP3 outstation/device itself.
Continuing our Tech Support Corner blog series, this post discusses what drives the polling behavior for DNP3 drivers in TOP Server and how the configuration on the device itself can impact what data is returned when a poll is issued.
Tech Support Corner: Configuring TOP Server as a Modbus Device/Server
8 min read
By Ganesh Kalipershad on Mar 2, 2023 2:00:00 PM
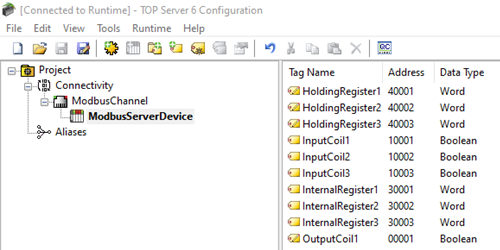
With Modbus having been around since 1979, I’m sure you have had some interaction with it or at least awareness of it if you work in the automation industry. Our TOP Server is very widely used for its Modbus TCP/IP Ethernet Driver and variety of Modbus serial drivers to enable users to connect to any Modbus devices that they have in the field. For that common use case, the device is the Modbus Server, and the TOP Server is the Modbus Client.
But what if you needed to configure TOP Server to be the Modbus TCP/IP Server (i.e. the “device”)? That is the purpose of this next post in our continuing Tech Support Corner blog series – to discuss and tell you how you can configure TOP Server to act as a Modbus server device, which is a common need for systems where either a device or other software application can only act as a Modbus Client and you have other systems that need connectivity to that Modbus client.
2023 Automation & Control Software Learning Resources
10 min read
By Kevin Rutherford on Jan 19, 2023 2:00:00 PM
Welcome to our most popular blog post of the year! This post is our 6th annual sharing of references to learning resources including new whitepapers, our ever hot Tech Support Corner, a new AVEVA Users Corner, and new technology releases that users have told us were the most helpful to them over the course of the last year.
2022 accelerated transformations as industry worldwide continued to adapt to succeed in the face of ongoing challenges in supply chain, inflation, labor shortages, and exploding customer demand. Each year we publish this blog post to help you learn, grow, and support empowering you to improve your business.
Understanding OPC UA Certificates and Certificate Authorities
5 min read
By Zachary Parham on Jul 14, 2022 2:00:00 PM
If you use OPC UA, you are likely at least somewhat familiar with OPC UA certificates. OPC UA client and server applications typically have Application Instance Certificates to provide application-level security. They are used for establishing a secure connection using Asymmetric Cryptography.
OPC UA certificates include a digital signature by the generator of the certificate. This digital signature can be self-signed or can be signed by a Certificate Authority (CA). Both types of certificates provide the same level of security and can be used in Asymmetric Cryptography. The major difference between CA signed and self-signed certificates in an OPC UA installation is the effort required to deploy and maintain the certificates. The choice of when to use a CA issued certificate versus a self-signed certificate depends on the installation and site requirements.
Many of our products leverage the OPC UA Configuration tool from the OPC Foundation to create and trust certificates and certificate authorities (CA). This tool actually installs with our OPC Data Client toolkit but is also available from the OPC Foundation. But how do we navigate this tool and the use of OPC UA certificates as a whole?
In this blog post, we will cover both methods of UA certificate signing, as well as the tool mentioned above for easily managing UA certificates for your OPC UA applications.
Tech Support Corner: How to Script Wireshark Capture
5 min read
By Rodrigo Restrepo on May 19, 2022 2:00:00 PM
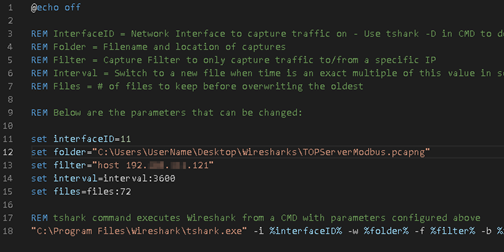
As you may be aware, Wireshark is an incredibly useful freeware tool for capturing network traffic on a computer. Our support engineers find it to be invaluable for troubleshooting Ethernet communications issues, as it provides visibility into more than just the protocol data packets, including handshaking calls and responses.
Wireshark also provides options for specifying capture filters (for defining a smaller subset of data to be captured that you're interested in) or you can capture all traffic and apply a display filter to narrow down the traffic that is visible.
Continuing our Tech Support Corner blog series, this blog post covers how to go even further using Wireshark by defining scripted custom Wireshark captures for specific use cases, which is helpful for capturing infrequent issues without wasting a lot of unnecessary hard drive space.
Tech Support Corner: Using PowerShell to Troubleshoot TCP Ports
4 min read
By Rodrigo Restrepo on May 5, 2022 2:00:00 PM
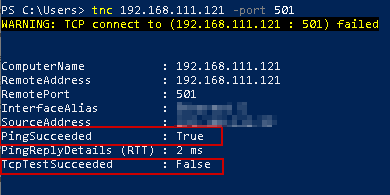
Do you find yourself in need of troubleshooting a TCP connection, but your IT department has everything locked down, so you're unable to install third-party Troubleshooting tools without permission? An often overlooked but effective tool for troubleshooting TCP socket connections is PowerShell.
Continuing our Tech Support Corner blog series, this blog post covers how to use PowerShell to effectively determine what issues you may be having with a problematic TCP Ethernet connection.
About this Blog
We're engineers like you, so this blog focuses on "How to" appnotes, videos, tech team tips, product update announcements, user case studies, and other technical updates. Subscribe to updates below. Your feedback and questions on posts are always welcomed.
Subscribe to our Blog
Recent Posts
Posts by Topic
- System Integrators (316)
- Device Connectivity (205)
- Wonderware (178)
- OPC UA (122)
- End User & Operator (120)
- Cogent DataHub (111)
- TOP Server (109)
- OPC (105)
- Technical Support (99)
- OmniServer (75)
- Video Tutorials (69)
- OPC Router (54)
- OPC DA (42)
- Protocols (40)
- AVEVA (37)
- Automation 101 (28)
- Security (26)
- MQTT & IoT (24)
- OmniServer Did You Know (24)
- Connectivity (23)
- Data Tunneling (23)
- OPC Data Client (22)
- IT/OT (20)
- Development Tools (19)
- DCOM (17)
- LGH (14)
- OPC Tunnel (13)
- Alarms & Notifications (12)
- Database (12)
- Earth Day (12)
- Summer of IoT (12)
- Exploring OPC UA (11)
- OPC Gateway (11)
- REST & Web Services (11)
- Case Studies (10)
- Dream Report (10)
- EFM (10)
- Oil & Gas (10)
- Reporting (10)
- CSV (9)
- Database & Historian (9)
- OPC Integration (9)
- OPC Server (9)
- Flow (8)
- Redundancy (8)
- Sustainability (8)
- AVEVA OPC UA Client (7)
- Modbus (7)
- OPC Router Basic Training (7)
- SuiteLink (7)
- DataHub Training (6)
- ODBC (6)
- OPC Alarms and Events (6)
- OPC Conversion (6)
- OPC Data Logger (6)
- ProtocolDesign (6)
- xml (6)
- Data Bridging (5)
- Data Logging (5)
- Data Storage Deep Dive (5)
- Industry 4.0 (5)
- Business Intelligence (4)
- Collaboration (4)
- Data Integration (4)
- InTouch (4)
- Industrial Decisions (4)
- OPC Bridge (4)
- OPC Redundancy (4)
- OPC Toolkit Benefits (4)
- OmniServer User Stories (4)
- SLIK-DA (4)
- SQL (4)
- Error Detection (3)
- IT & Infrastructure (3)
- OPC Server Remote Config (3)
- Wedges (3)
- Windows (3)
- ControlLogix (2)
- Excel (2)
- Ignition (2)
- Industrial AI (2)
- KEPServerEX (2)
- Kepware Edge (2)
- New Release (2)
- OPC Wizard (2)
- OSIsoft (2)
- Omron (2)
- PGAS (2)
- Predictive Maintenance (2)
- Process Alert (2)
- Scripting (2)
- Store and Forward (2)
- Building Automation (1)
- ERP (1)
- LGH User Stories (1)
- LRC (1)
- Linux (1)
- Machine Learning (1)
- Mining/Metals (1)
- N3uron (1)
- Omni Flow (1)
- Power & Utilities (1)
- Predictive Analytics (1)
- Process Alerts (1)
- QNX (1)
- Sparkplug B (1)
- Water & Wastewater (1)