Though you may have never needed to contact Software Toolbox for support, it’s always smart to be ready for any challenges that might arise. That’s why it’s helpful to know the resources you have at your disposal, should you ever need to connect with our experienced support team to overcome any challenges when using our solutions.
At Software Toolbox, we are committed to providing our users with timely and high-quality responses to their support incidents. While your question or issue might not always be completely resolved after the first response, you can expect to receive our initial response within 2 regular business hours after submitting a question, although it often happens much sooner! We even have some tools that can help speed up this process.
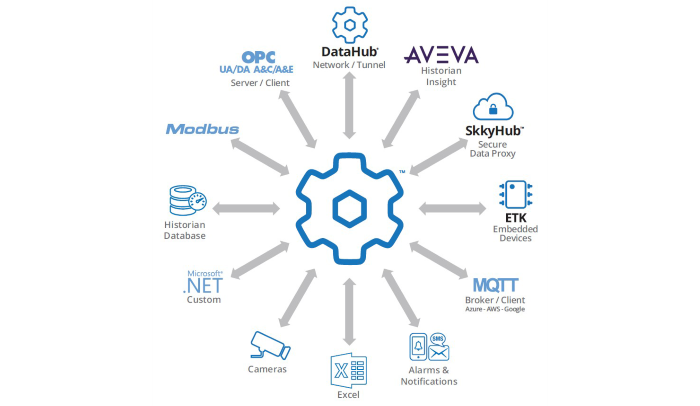
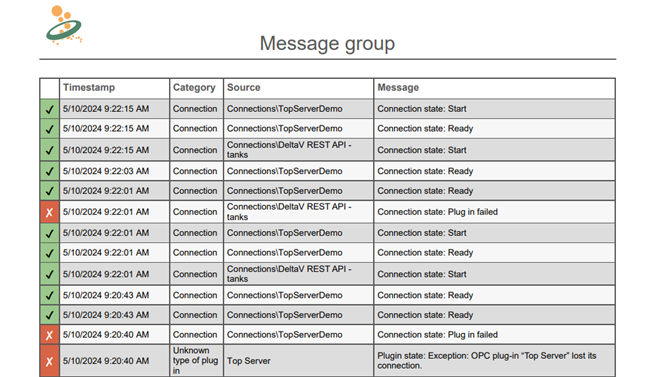
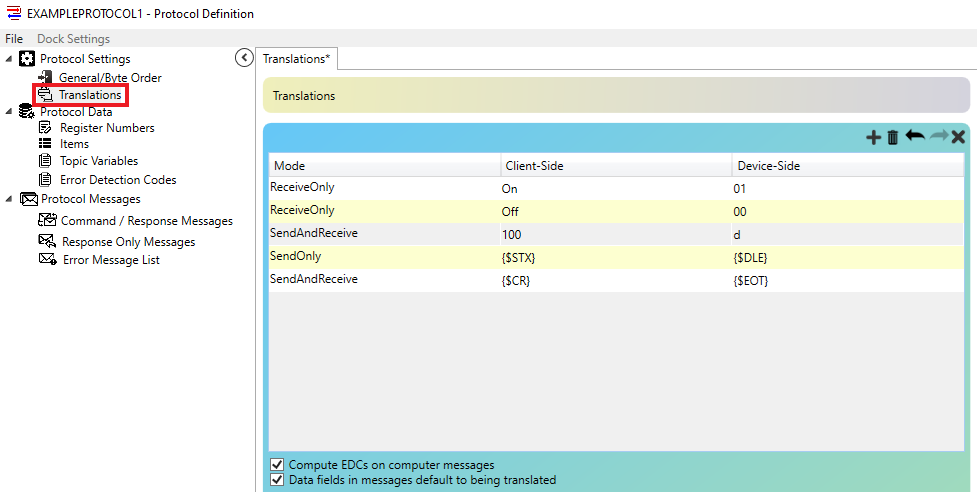
As a part of our Tech Support Corner blog post series, this blog post covers how the OPC Router’s Application Report helps us help you by allowing you to provide much of the information that we need to troubleshoot issues when you initially contact us.